The rapid increase in remote workforces and growing edge locations is driving the need for more secure data centers. To safeguard your IT infrastructure investment, count on a trustworthy network partner to reduce the risk of unauthorized users accessing the critical infrastructure as well as maintaining secure, classified data. Vertiv provides remote network and data isolation security solutions that are easy to manage without compromising accessibility.
Benefits of Secure Remote and Local Access
Security and Compliance
Prevent unauthorized users from accessing your critical IT infrastructure and keep secure data secure. With various levels of security requirements both within and outside the data center, it’s important to install the most up-to-date technology in the market.
Cost Reduction
Keep truck rolls to a minimum and keep desks clear of multiple KVM devices. With secure, remote ACS dial-in access and secure desktop switches, keep costs down and productivity up.
Secure Access
Within any organization, security needs to take on many looks. Organizations require secure access to keep business up and running, and many need to ensure that various levels of classified data is not compromised. With the secure KVM switches and secure ACS access, you decrease the risk of bad things happening.

Data center owners and operators are bringing on new capacity to meet voracious business demand and enable business’s digital transformation. In the U.S. alone, there are 526 megawatts under construction.
Server Management Security, Remote Access And Control With Avocent® ACS
TheAvocent® ACS Advanced Console System offer the performance and reliability necessary to efficiently access and manage IT assets. Learn how the ACS can help you increase efficiency and security in the data center and remote branch office environments.
View Avocent® ACS 8000 Serial Consoles
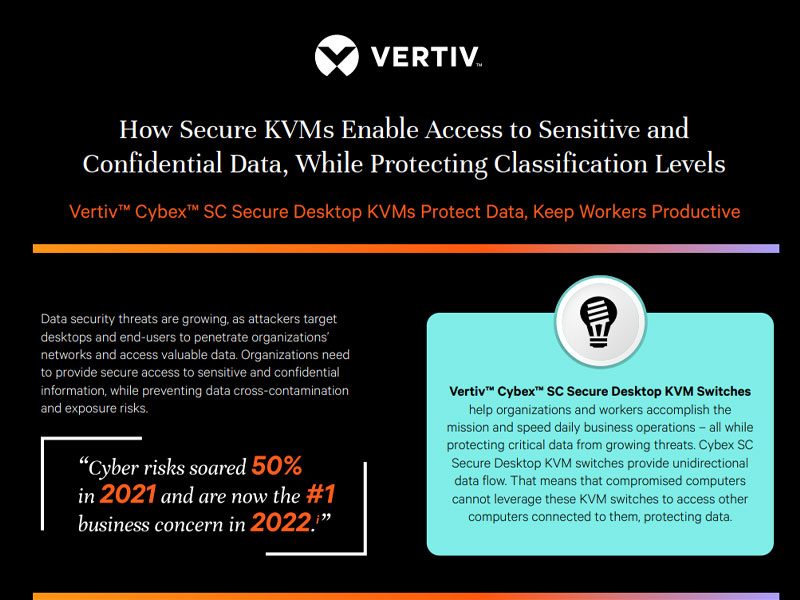
The Vertiv Cybex Secure Desktop KVM Switches
All Vertiv™ Cybex secure switches are designed to stringent specifications for keeping data secure, allowing users to switch safely between computers operating at different classification levels, which provides continuous access to critical data in a secure, sensitive environment.
Certified Secure KVM Switches
Securely manage classified and non-classified projects simultaneously with KVM switches, which ensure the protected access you need to peripheral sharing devices. Interact with multiple computers or displays with zero delay switching. Vertiv’s KVM switching portfolio offers numerous options that reduce the risk of data contamination.
- Vertiv Cybex Secure Desktop Mutiviewer
- Vertiv Avocent ACS8000
- Vertiv Secure Desktop Matrix Switch
Insights
How can we help?
Please fill out the form below, send us your question(s) and we will get back to you as soon as possible.
Thank you! Submission has been successfully sent.






