Risks and Recourse from a Director of Security Operations
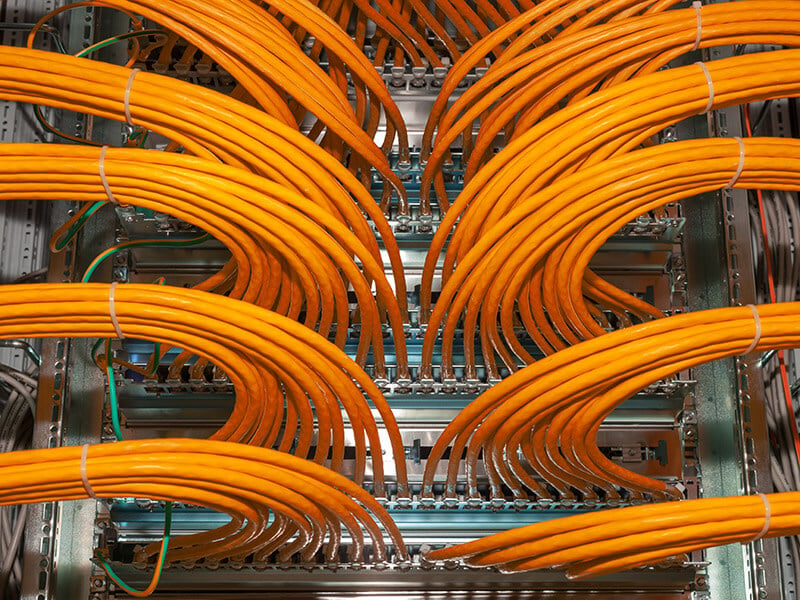
In an era of digital transformation, companies have taken a defense-in-depth approach to securing networks. This means that information security teams leverage a variety of controls, processes, and tools to identify and address issues early and often, with the goal of stopping cyber attackers from exploiting gaps and vulnerabilities. It’s a challenging endeavor that’s never done.
Now, with a global pandemic requiring shifts in workforce needs, new risks are emerging, and threat patterns are changing. This is requiring input from collaborators old and new. Network protection now requires close cooperation from information security, IT, business continuity, disaster recovery, and crisis management teams.
“A computer virus spreads much like a pandemic virus, with both having significant impact on a business,” says Kate Fulkert, Business Continuity and Disaster Recovery Manager at Vertiv. “This is why business continuity and security teams need to be tied at the hip for the foreseeable future.”
Mike Spaulding, Director of Security Operations at Vertiv, sees the following risks and threats emerging worldwide:
Risk #1: Company Networks Are Under Siege
The pandemic has challenged companies’ business continuity, as many weren’t prepared for their workforce to go fully or mostly remote. Many IT teams are developing a virtual desktop infrastructure (VDI) at top speed so that their companies can adopt Desktops as a Service (DaaS) platforms. They’re also reviewing additional applications and workloads that can rapidly move to the cloud to improve business continuity and performance.
Despite business pressures, we recommend that companies invest ample time for security during this process. As companies build their VDI, they should carefully review their network connections, capacity needs, firewalls, and other security requirements. Many applications will need the security of a virtual private network (VPN) while others can be migrated to the cloud for direct access.
Organizations in regulated industries, such as financial services and healthcare, will obviously have more stringent requirements for their hybrid cloud strategies when compared to other verticals. For those starting their cloud journey, data backups, batch processing, and disaster recovery can provide immediate value, strengthening business continuity. Others facing capacity constraints may choose to ramp up Infrastructure as a Service (IaaS) and Platform as a Service (PaaS) deployments.
An Avalanche of New Attacks
Companies are always bombarded with threats, but the number varies. In a recent Cisco security survey, 17 percent of companies say they receive 100,000 or more security alerts every single day, leading to cyber fatigue. Remote monitoring and AI-driven security information and event management (SIEM) solutions can help identify real threats from false alarms, as well as help prioritize them. Remote monitoring can also help IT teams track data center health, such as evaluating the condition of power and cooling systems and enabling workers to proactively replace systems and parts that demonstrate signs of stress before those issues lead to critical failures.
Risk #2: Employees Introduce Risks into Networks
Phishing is an ongoing challenge for companies, because people are typically easier to exploit than networks. A Wombat Security study found that 83 percent of respondents experienced phishing attacks in 2018 and 49 percent experienced vishing (voice phishing) and/or smishing (SMS/text phishing). Phishing emails have spiked over 600 percent since late February as attackers seek to capitalize on employees’ fear and confusion around world events and new work-at-home practices.
Here are some phishing risks of which you should be aware, especially during this unprecedented time:
- Brand impersonation: Bad actors are impersonating authority organizations, such as the World Health Organization, the Centers for Disease Control and Prevention, or Internal Revenue Service. Employees may receive professional-looking emails with updates and be directed to click on seemingly authentic websites or download attachments with malware.
- Authority figure impersonation: Attackers may send targeted emails, impersonating business functions such as IT, human resources or finance. They may also pose as individuals such as a company’s chief executive officer. These emails often direct recipients to download a malicious file. Examples could include a company’s latest updates on current world news or an announcement of new IT and payment processes.
- Pandemic-related scams: These requests which are more obviously aimed at access to finances can include shopping websites offering hard-to-obtain products such as masks and hand sanitizer; medical organizations seeking payment for a friend or relative or offering insider access to a vaccine or drug; airline and hospitality businesses offering refunds; and charities appealing for contributions. The goal of these attacks is to persuade employees to pay for a fraudulent good or service they’ll never receive or solicit funds for a non-existent charity.
We recommend that companies provide communications on the latest phishing strategies — how to recognize and avoid them, and how to report attacks. Now is a good time to refresh information on what to do in the event of any security incident and remind employees that it is everyone’s duty to protect the company with timely reporting.
Weak Controls
As employees work from home, they’re accessing company resources on their own devices and Wi-Fi networks. This can introduce risks to the company network when employees use default or easy-to-guess passwords; use Wi-Fi networks and devices that aren’t encrypted; perform work and personal surfing on the same devices; and neglect downloading software updates and security patches.
We recommend that companies provide tip sheets to help employees do basic IT hygiene before connecting to company networks. Any application that has single-factor authentication (passwords) should be disabled until it can be replaced with multi-factor authentication. In addition, companies should review administrator access privileges to make sure they’re current and limited to only the systems the IT team needs to do its job. As information security teams know, administrator privileges are the holy grail for cyber attackers, because they enable pervasive access to networks.
Risk #3: Customers and Partners Can Experience Threats
Cyber attackers often target third parties because they have weaker security than their enterprise customers and often have privileged access to email, systems and files. Ponemon Institute found that 59 percent of companies had experienced a data breach because of a third-party.
In addition to performing regular risk assessments of key vendors, enterprises should require multi-factor authentication for third parties, reinforce the policy of least access granted, and automatically discontinue network access when it is no longer needed to reduce the possibility of a breach.
Customer Fraud
Customers may be targeted by attackers who compromise emails for man-in-the-middle attacks. Bad actors impersonate vendors and partners by sending seemingly authentic emails, making targeted phone calls, and providing fraudulent payment information. When high-dollar purchases are at stake, attackers will play the long game, engaging with targets through a multi-month B2B sales cycle with the goal of getting a large wire transfer.
We recommend that companies communicate with customers immediately to share these new attack patterns and reiterate their company’s key marketing, sales, and financial practices. If customers have any concerns about invoicing or payments, they will then be able to contact key representatives directly.
With the recent and rapid shift in companies’ working models highlighting IT network vulnerabilities, now is the time to strengthen the security of your systems and empower your employees to identify and report threats.
As always, Vertiv is here to help. If you need service, parts, or technical support, please contact your Vertiv representative.